Configuring SCIM in Microsoft Entra ID
Instructions for configuring SCIM provisioning in Microsoft Entra ID. SCIM allows you to enable seamless and automated user management across your applications.
Prerequisites
Before you start, do the following:
- Learn about the SCIM configuration process in Configuring SCIM.
- Configure single sign-on (SSO) with Microsoft Entra ID as an identity provider. For instructions, see Configuring SSO with Entra ID.
- Get a long-lived access token through the MTM API. For instructions, see Get a Long-Lived Access Token.
Configuring User Provisioning
Follow these steps:
-
In Microsoft Entra ID, navigate to the SSO application for SAP LeanIX.
-
On the Provisioning page, configure provisioning settings.
-
In the Provisioning Mode list, select Automatic.
-
Under Admin Credentials, in the Tenant URL field, enter the following URL:
https://{SUBDOMAIN}.leanix.net/services/mtm/v1/scim/v2 -
In the Secret Token field, enter the long-lived access token that you obtained.
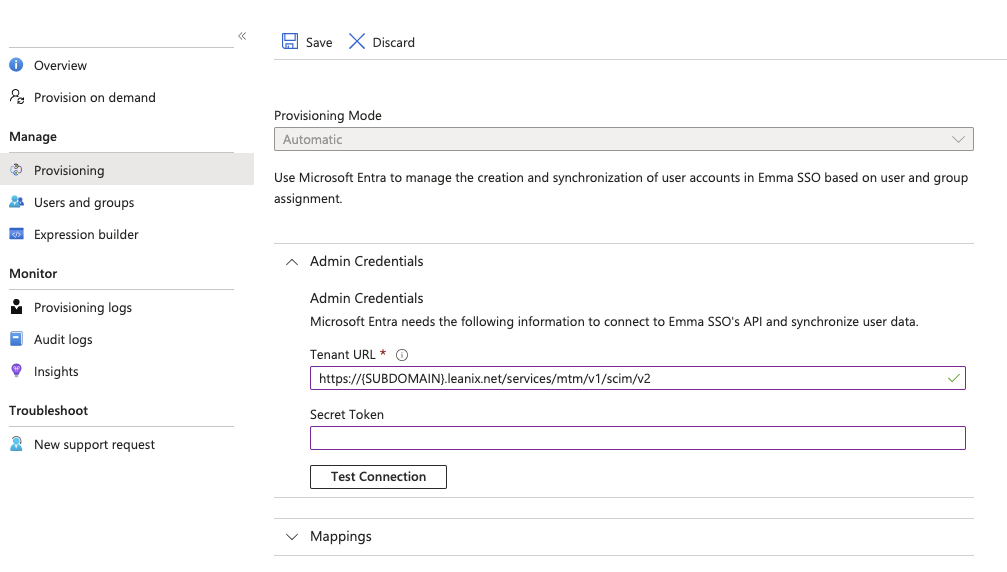
Configuring Provisioning Settings in Microsoft Entra ID
-
Under Mappings, ensure that provisioning for Active Directory Groups is disabled.
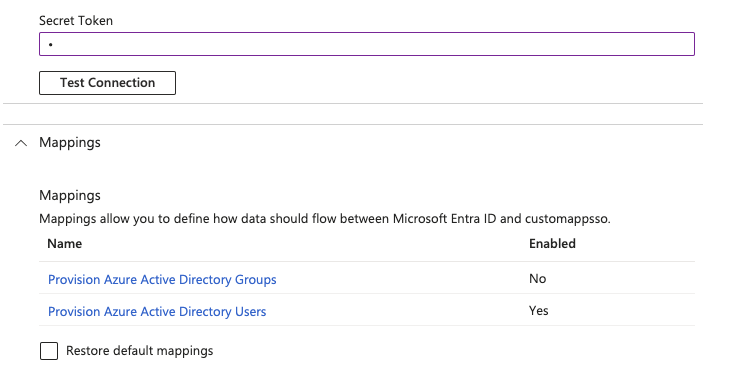
Mapping Settings on the Provisioning Page
-
-
On the Attribute Mapping page, update attribute mapping to include only the following attributes and delete all other attributes.
-
userPrincipalName: Please ensure that the property you're passing is identical to your SSO configuration. Change the SCIM property as needed. This property must be in the email format. -
mail -
Switch -
givenName -
surname -
department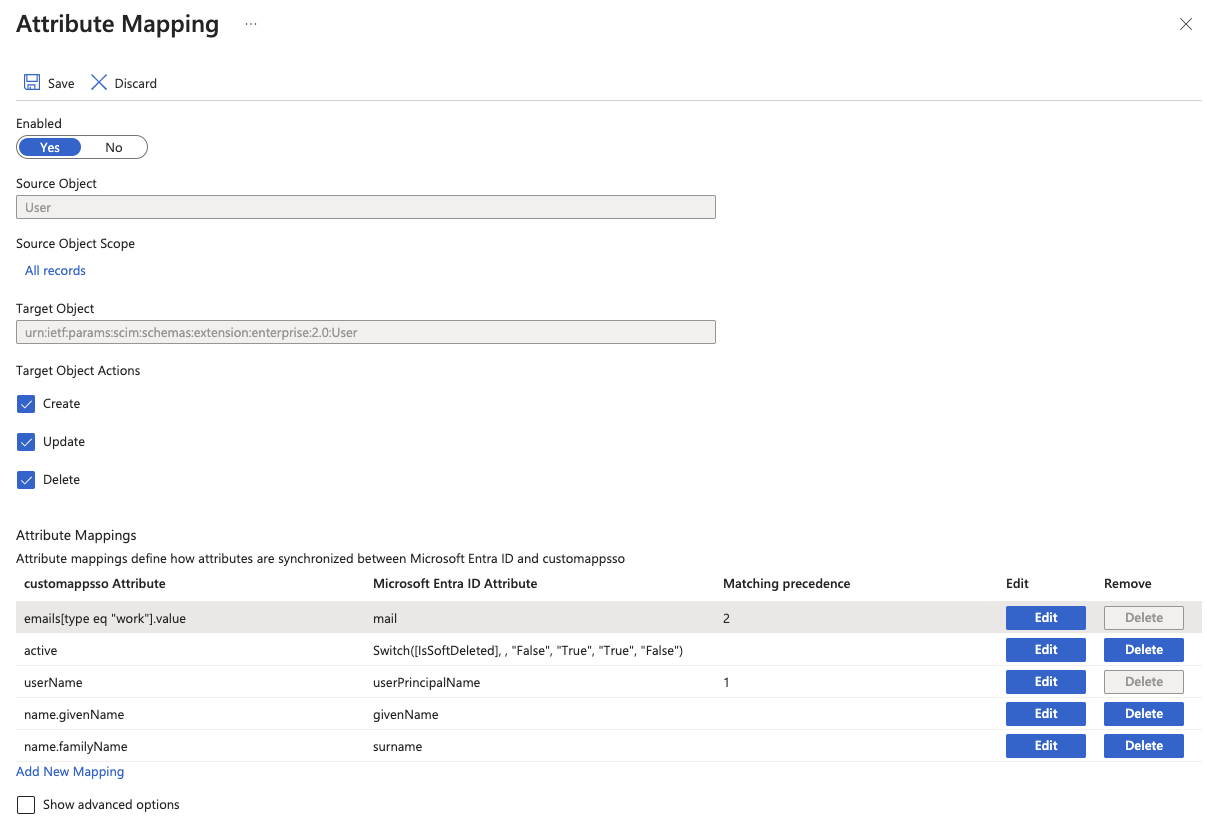
Required Attribute Mappings for SCIM Provisioning Between Microsoft Entra ID and SAP LeanIX
To make Entra ID compatible with the SCIM implementation, configure the predefined email attribute as a matching attribute with the Matching precedence set to 2.
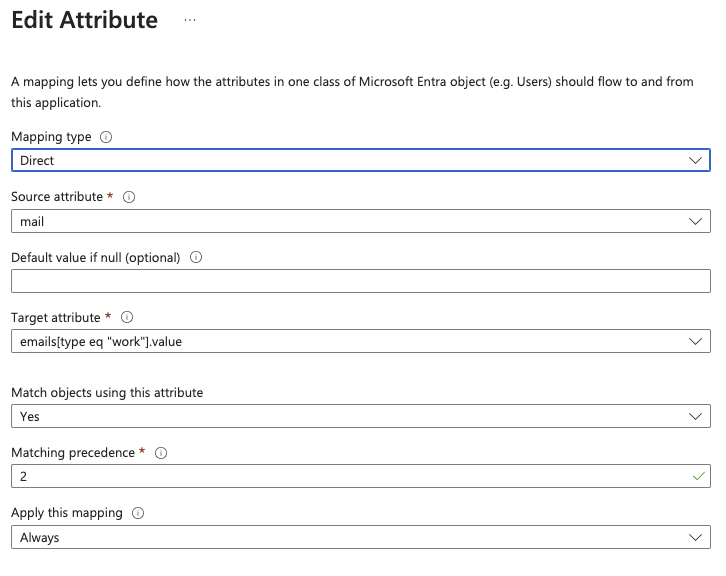
Configuring the Email Attribute
Note
To learn more about attribute mapping and SCIM provisioning, refer to the Microsoft Entra ID documentation:
-
-
To test provisioning, select Provision on demand and enable provisioning for a test user.
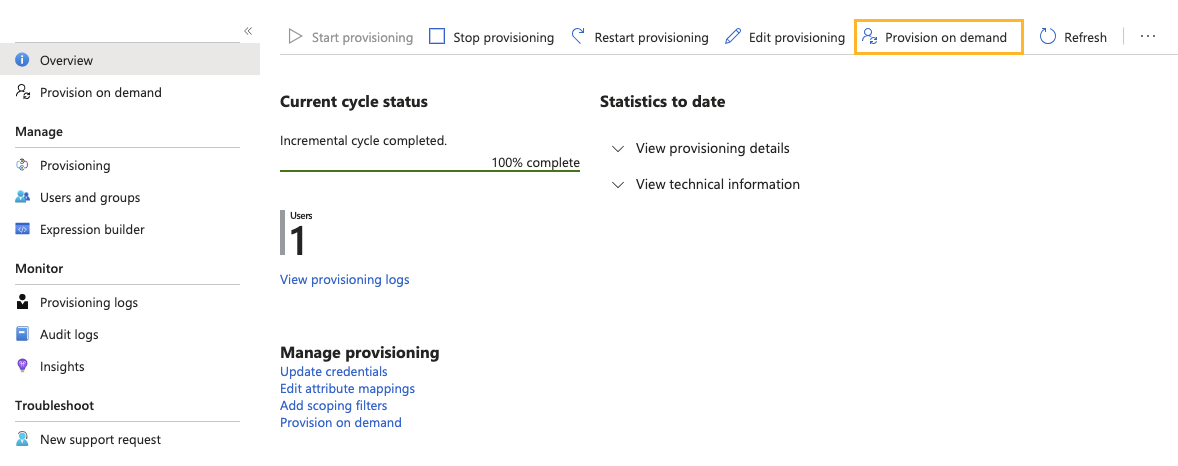
Selecting the Provision on demand Option for Testing the Configuration
-
After you've tested provisioning for a test user, click Start provisioning.
SCIM provisioning between Microsoft Entra ID and SAP LeanIX is enabled.
Configuring Externally Managed User Roles
If your organization manages user roles externally within Microsoft Entra ID and not within SAP LeanIX, create an attribute for the role property. To learn more about managing user roles, see Managing User Roles with SSO.
Follow these steps:
-
On the Attribute Mapping page, select the Show advanced options checkbox, then select Edit attribute list.
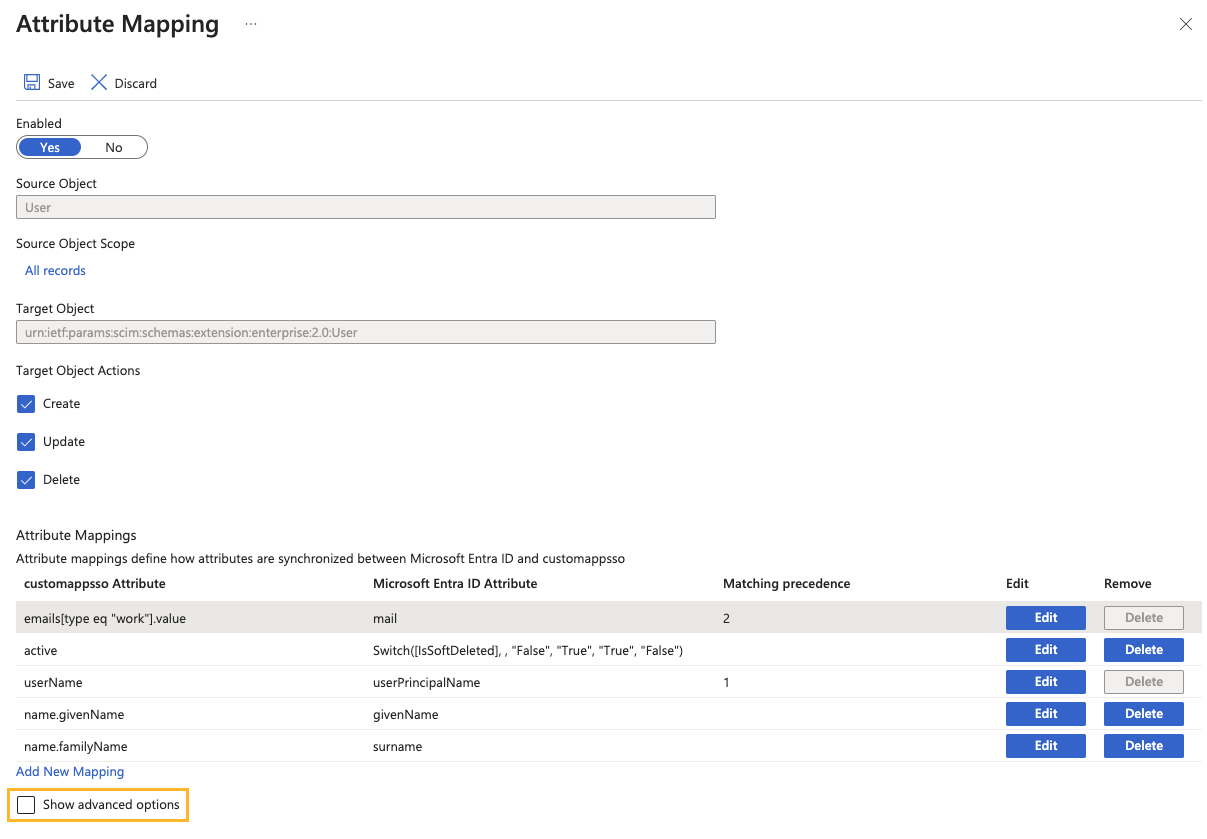
Navigating to Advanced Options from the Attribute Mapping Page
-
On the Edit Attribute List page, create a new attribute for the role property using the following string:
urn:ietf:params:scim:schemas:extension:workspacePermission:2.0:User:role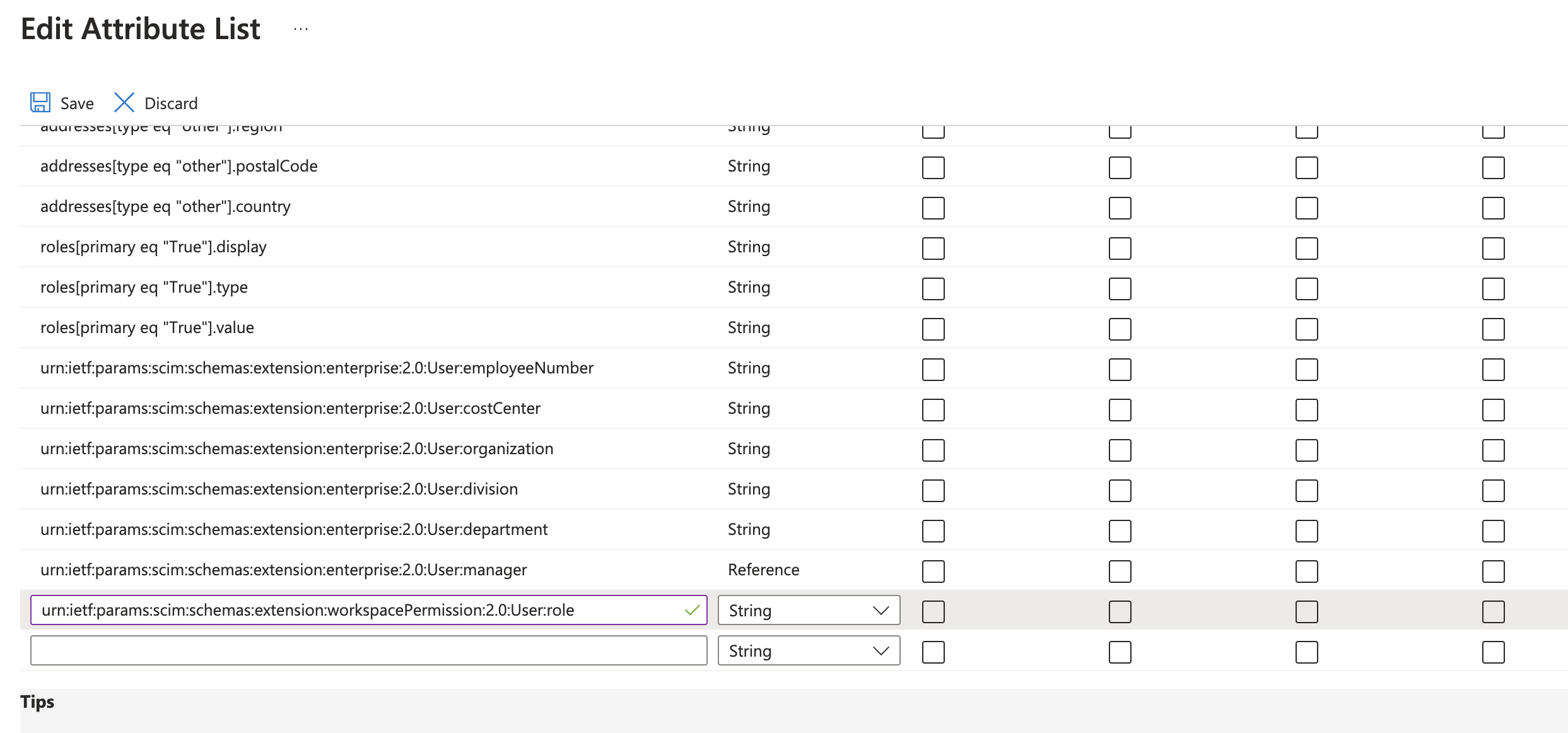
Creating an Attribute for the Role Property
-
On the Edit Attribute page, configure mapping for the attribute, then save the changes.
-
In the Mapping type list, select Expression.
-
In the Expression field, enter the following:
IIF(Instr([appRoleAssignments], "ADMIN", "", "")>"0", "ADMIN", IIF(Instr([appRoleAssignments], "MEMBER", "", "")>"0", "MEMBER", IIF(Instr([appRoleAssignments], "VIEWER", "", "")>"0", "VIEWER", "")))
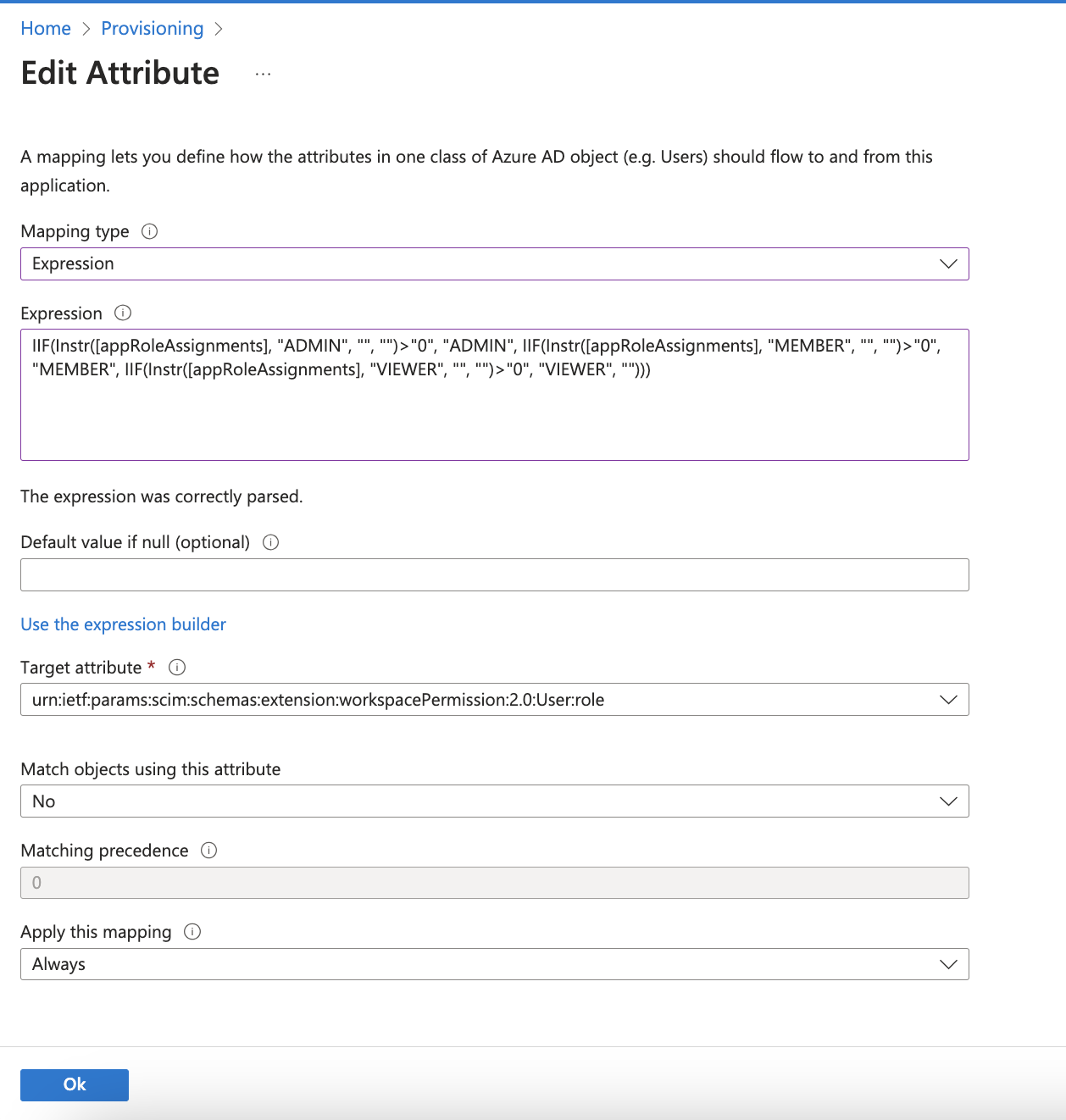
Configuring Mapping for the Role Attribute
-
User role mapping between Microsoft Entra ID and SAP LeanIX is enabled.
Updated 8 months ago
